Magento Images Broken after Upload
I recently updated a few sites using Magento with the new security patch 7405 (note that link is for the patch info – not a download – more on that later). After the update any images uploaded or added resulted in a broken image link.
I was able to troubleshoot and while looking on the server, the uploaded images were in the proper directory, however they were still not showing on the site.
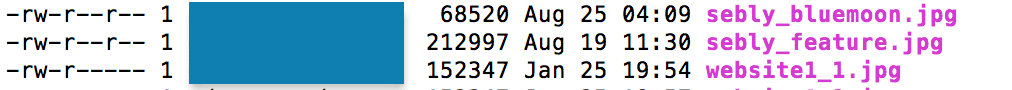
After finding the images, I started to troubleshoot the permissions. It appears that they were set at a 640 level and not readable by anyone. The 640 permissions (rw-r—–) equate to the owner having read and write permissions, the group has read permissions, and all other user have no rights to the file. This was in interesting find, as any image uploaded through the admin we would want at least readable.
I changed the permissions of the image to 644 – (rw-r–r–) The owner will have read and write for the file, while all others may only read the file. You can see an example of a image previously uploaded and one uploaded with the permissions after the patch (good – selby_feature.jpg, not working – website1_1.jpg)
chmod 644 somefile.jpg
Magento Patch Permission Changes
From this error I started doing some investigation it appears that others are having this issue. It was referenced on a few posts.
https://community.magento.com/t5/Security-Patches/after-installing-SUPEE-7405-can-no-longer-add-or-change-images/td-p/26785/page/3
There are a few good discussions on the best way to address this permission change. Apparently the permissions have been changed to address PCI concerns. From my understanding this change would keep Administrators / Content editors from being able to upload malicious scripts to be executed.
From the different methods discussed I selected to edit the upload.php file. There are 2 ways to do this: 1. Overwrite the main file, 2. copy the file to a localized version (overload). I selected option 1, as I did not want to have to reconcile files with the overloaded file with any update or patch.
The fix I used
I will now describe the fix I used.
1. First fix all the existing uploads. You need to change all existing uploaded images permissions from 640 to 644. You do this with the following command chmod 644 yourimagefilename.jpg
2. To create a more permanent fix and allow for any future uploaded image you need to edit the file Uploader.php. You can do this via ftp and then edit the file.
The file is located at
/lib/Varien/File/Uploader.php
The area I changed was at line 219 and another edit at line 541.
Change the file permissions from 640 to 644
Offending code at line 219chmod($destinationFile, 0640);
Change to:
chmod($destinationFile, 0644);
To change the Directory Permissions from 750 to 755 at line 541
Change from: if (!(@is_dir($destinationFolder) || @mkdir($destinationFolder, 0750, true))) {
Change to:
if (!(@is_dir($destinationFolder) || @mkdir($destinationFolder, 0755, true))) {
The update and test this process. You can view the file I modifed here
https://gist.github.com/JimBecher/59cf97d0ddb1c526f25d
other options
There are other options to fix this challenge. This other proposed option is to determine the user that the webserver runs as and then set the permissions on the folder and file to that user. I did not know the proper technique to make that happen in the environments I have Magento running. It sounds like many others also have a similar problems with this approach.
Secure Your Magento – Patch Today
If you have not patched your system, please download and run the patch. This link will take you to the area to download the patch and you will need to select the version of Magento you have installed. I wish the Magento team would do two things in their security / patch model. 1. Allow that patch info page to have a direct link to the patch (Note: the big get the patch button just takes you to info)
2. Allow people to download patches with out having to log in. The reason for allowing downloads without login is so users can use wget on a server to get the bits.
Thanks, good luck patching.