Configure IIS to use – X-Frame-Options
I recently had a request to update a server to correct a few audit findings. One finding was related to “clickjacking” (More info from Wikipedia and OWASP) Clickjacking is a process where a malicious link is injected on the page that takes you to what you would think is a normal page but is hijacking your browser.
In reading the finding and the OWASP write-up the best course of action for an IIS server was to utilize the X-Frame-Options. The X-frame-options concept came into play during the time of IE-8. The Microsoft team has a nice write up – https://blogs.msdn.microsoft.com/ieinternals/2010/03/30/combating-clickjacking-with-x-frame-options/
This was then introduced as a standard in 2013 (take note some browsers do not have full capability with a particular setting)
IIS Settings – Clickjacking
To correct the audit finding, I took advantage of using the IIS header configurations https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options.
You can modify these directly in your (web.config) for IIS, this is located in the root of the site. This can be added in your existing
[cc lang=”php”]
[/cc]
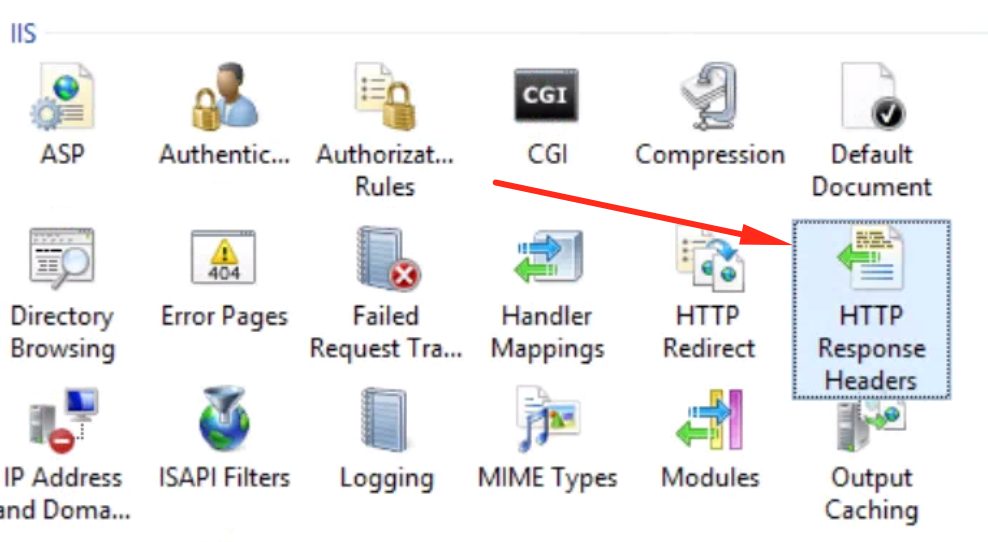
Or the easier method, that I ended up using was to change this directly in IIS manager. There is the ability to update the Header right through the GUI.
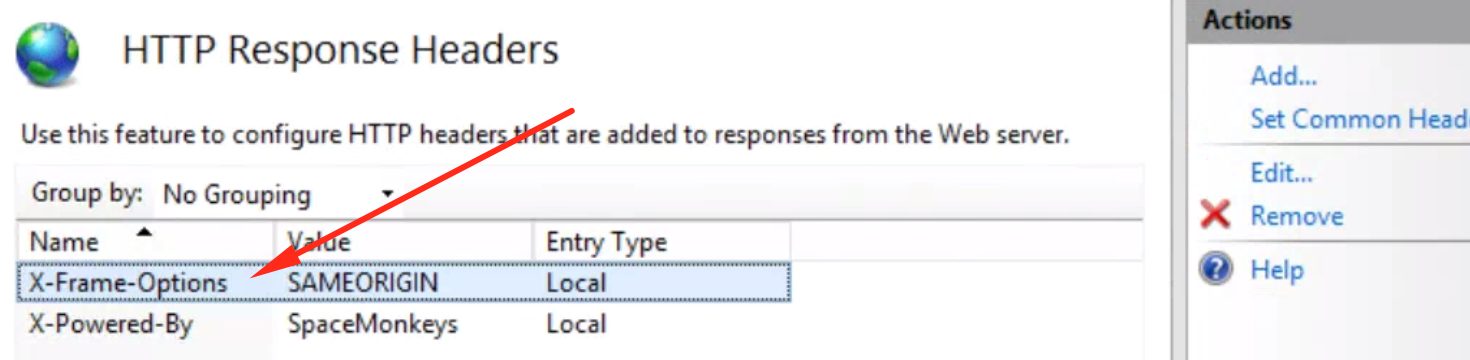
Select the HTTP Repsponse Headers and select the Add link. Create a name “X-Frame-Options” and add a value of “SAMEORIGIN”
When you edit this in IIS Manager it will add the elements to the “Web.config” in the root of your website.
While doing this change I also modified the X-Powered-By settings to remove .net.
Changing this header option will protect your side from the Xforwarded Clickjacking. Reminder you need to make these changes to the Server and not in your page with tags.

